If you've encountered error messages like "Cannot conclude handshake. Cause: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find a valid certification path to the requested target" or "System error: server certificate verification failed. Connection aborted," these denote that the SSL Certificate of the site is not being trusted by your system. This does not normally indicate a problem with the service you’re connecting to, but it does mean additional configuration will be required. You should also double-check that these errors are expected within your organization as these can be a sign of a malicious actor attempting to hijack your connections.
This article guides you through the steps to address this SSL certificate trust issue.
Resolution Steps:
Once you’ve ensured that this is expected from your service, take the following steps to resolve this problem. You will first need the public SSL Certificate. If don’t already have this, you can get it from our log file:
-
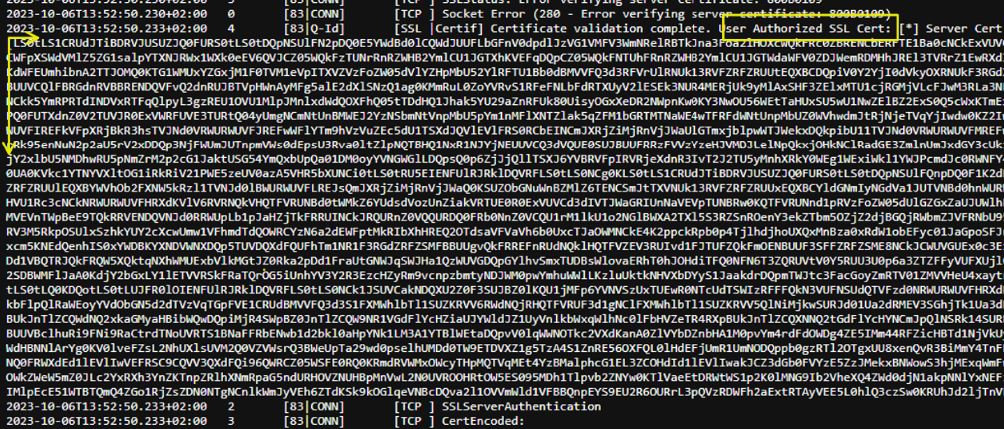
Set the verbosity of your log file to level 4 and attempt to establish a connection.
-
After generating the log file, locate the "User Authorized SSL Cert" section, which appears as a value inside square brackets.
-
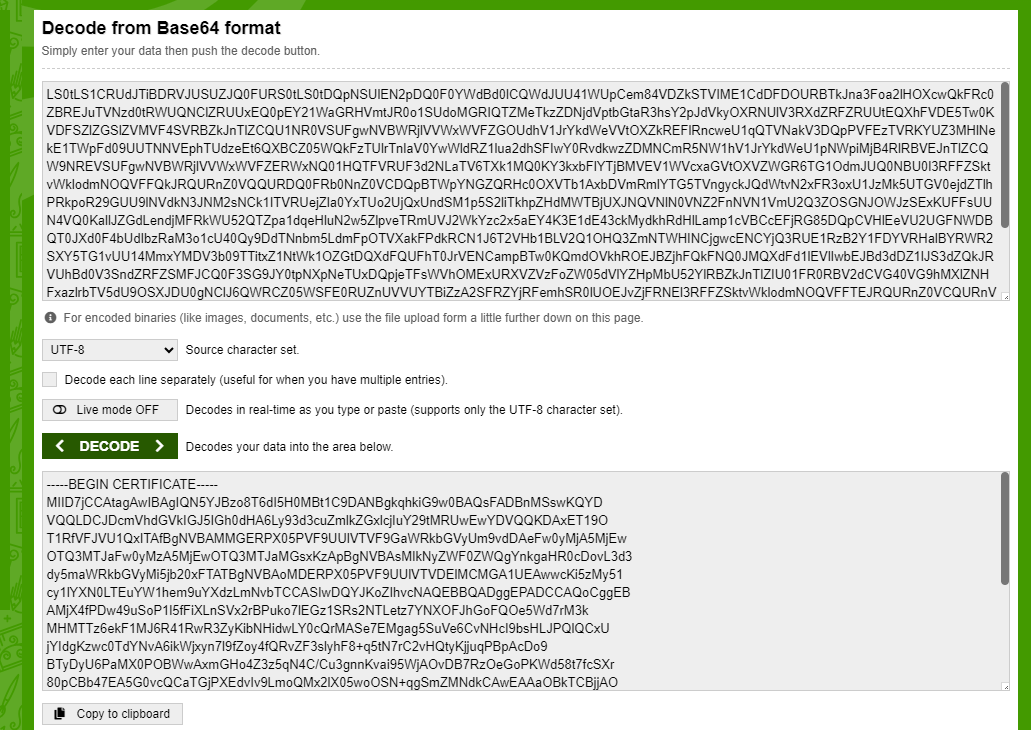
Copy the contents inside the square brackets and decode them using a base64 decoder to obtain their proper value. It should look like this:
Now that you have the SSL certificate, take one of the following actions:
1. Replace SSLServerCert Value:
-
In the SSLServerCert field, paste the content obtained from the previous step.
-
Ensure there are no trailing spaces.
-
This step allows you to connect without SSL certificate trust issues.
Example: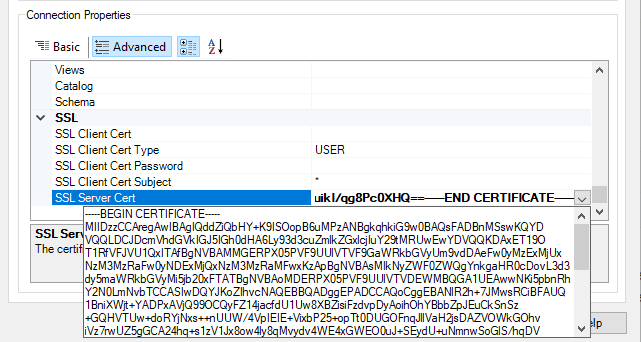
2. Convert to .pem or .cer File:
-
You can also create a .pem or .cer file in Notepad, input the content, and save the file.
-
Specify the path of the file in the SSLServerCert property
Example: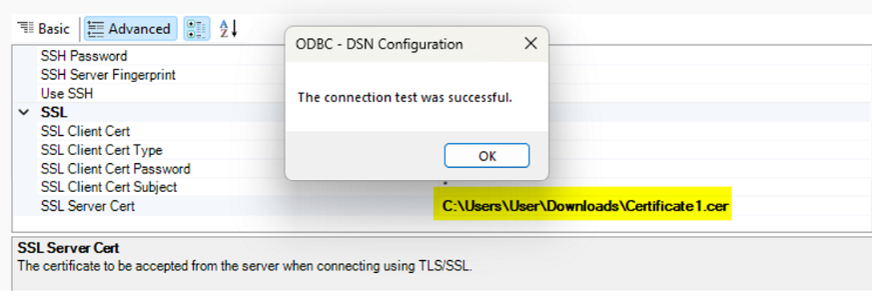
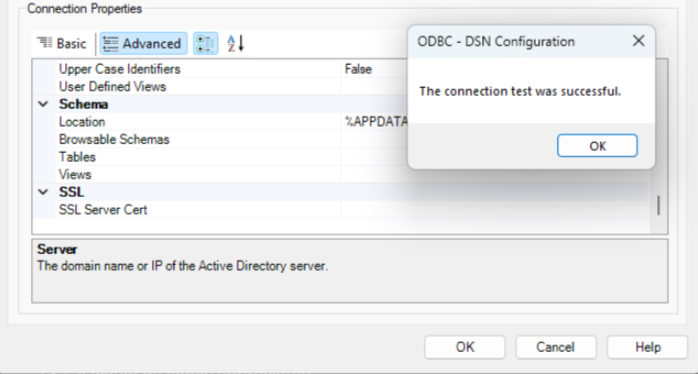
3. Import Certificate from Trusted Root Certification Authorities:
-
Alternatively, you can import the certificate file from #2 (.cer) into the Trusted Root Certification Authorities to establish trust. The example below is how you store the certificate for ODBC, ADO.NET, and SSIS. For Java-based applications such as JDBC, the certificate must be placed in the JVM trust store.
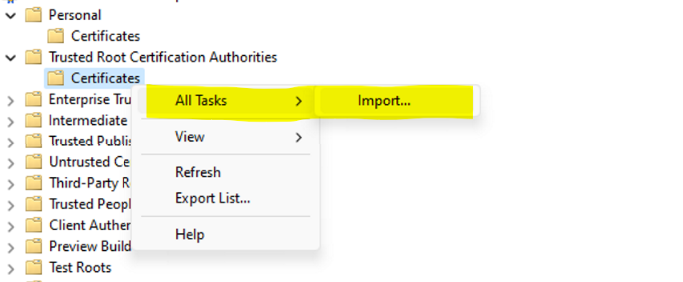
-
After importing the certificate in the Trusted Root store, there should be not any other configuration on the driver side regarding the certificates.
---
One additional way to address this issue just for testing is by setting SSLServerCert=* which instructs the driver to accept any SSL certificate and will therefore avoid the error.
WARNING: This option will disable SSL certificate validation and thus creates a security vulnerability. This should only be used temporarily for testing purposes rather than as a permanent solution.
If you continue to face issues after following these steps, do not hesitate to contact CData support ([email protected]) for further assistance and troubleshooting.