There are several data sources (Workday, Google BigQuery) that require HTTPS connectivity, in order to define a successful source/destination connection within CData Sync.
By default, Sync is installed as HTTP web server, however there is also the opportunity to configure it and expose the server as HTTPS endpoint.
This article explains how to enable SSL/TLS connectivity for CData Sync.
Step 1: Verify the existence of “sync.properties” file within Sync installation directory
There might be situations where “sync.properties” file does not get generated after the successful installation of CData Sync. If the file is missing from the installation directory, then open the terminal in that path and run the following command:
java -jar sync.jar -GenerateProperties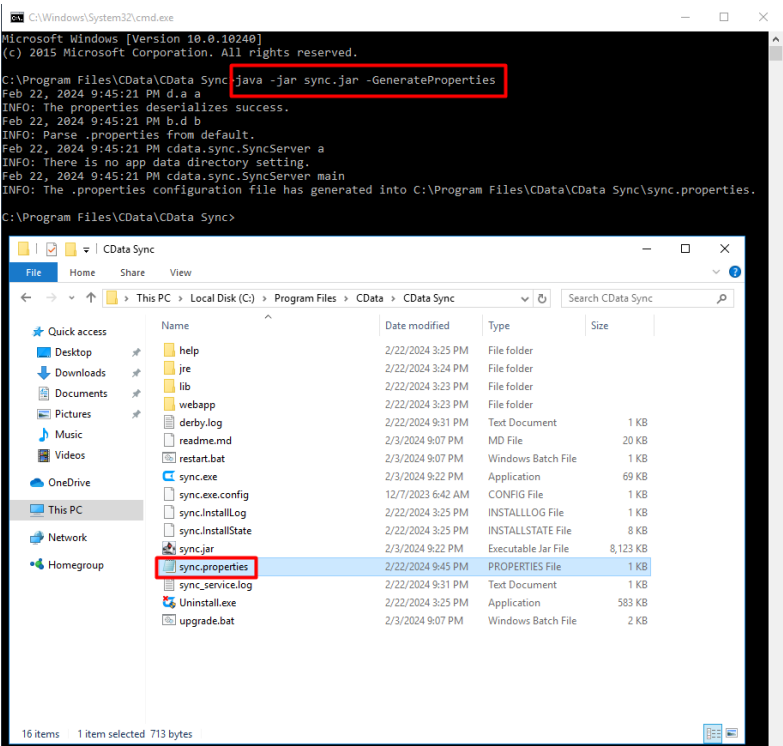
Step 2 (optional): Generate a self-signed certificate
This step can be performed if there is not any CA certificate to be used for such operation. Instead, a self-signed certificate can be defined in “sync.properties” file. In order to generate a self certificate via OpenSSL, the following commands should be executed within the terminal:
1) Generate RSA private key
openssl genrsa -out ca.key 4096
2) Sign the certificate
openssl req -x509 -key ca.key -out ca.crt -days 365
3) Convert to PKCS12 (.pfx)
openssl pkcs12 -export -in ca.crt -inkey ca.key -out ca.pfx
Step 3: TLS enablement
To enable SSL/TLS connections (HTTPS), you also need to modify the sync.properties file in InstallationDirectory, as follows:
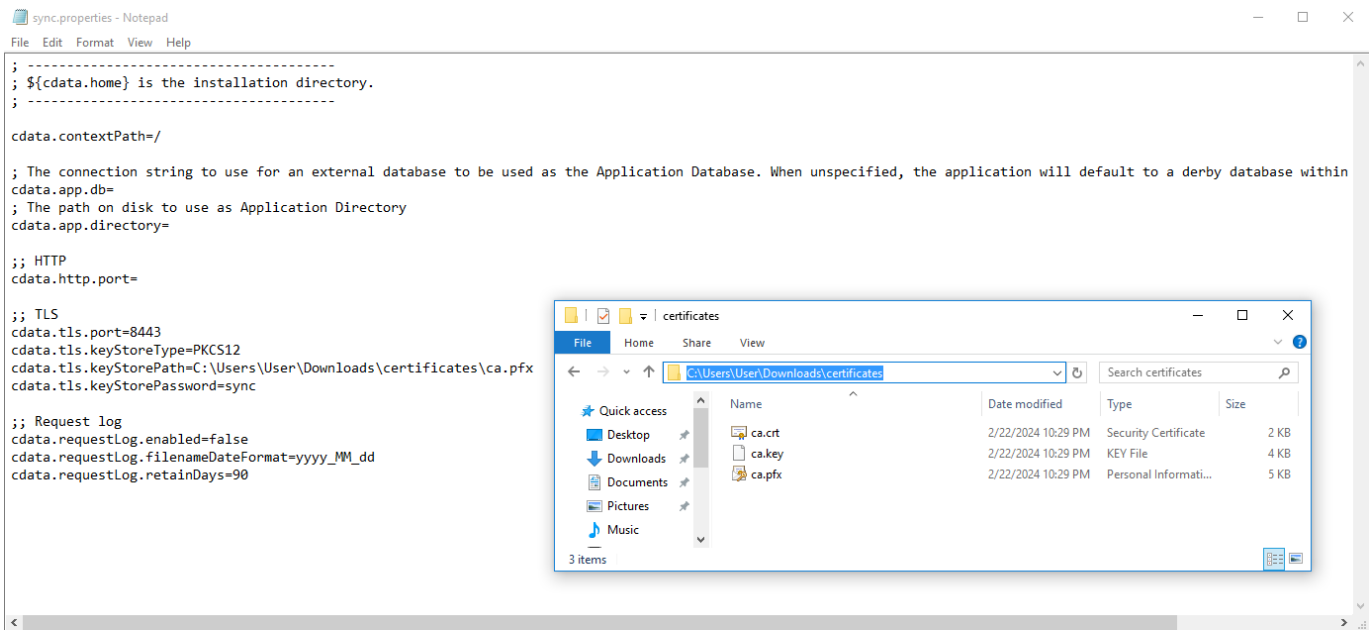
- Set the “cdata.tls.keyStoreType” setting to the type of keystore that will be used. Valid values include jks, pkcs12, and jceks.
- Set the “cdata.tls.keyStorePath” setting to the path of the keystore that will be used. Note that ${cdata.home} might be used to refer to InstallationDirectory
- Set the “cdata.tls.keyStorePassword” setting to the password for the keystore
- Set the “cdata.tls.port” setting to the port that should be used to host the server
(Optional) Set the “cdata.http.port” setting to an empty string to disable plaintext connections.
The final result should look like this:
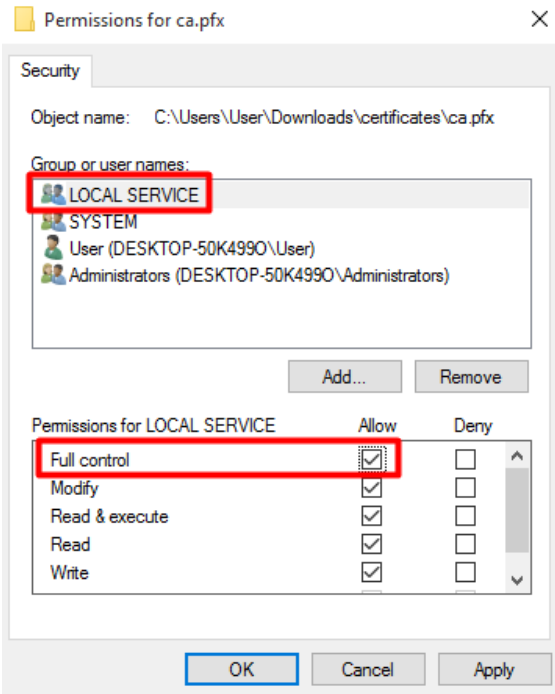
Step 4: Update user permissions for the certificate
Since Sync is compounded by a service that handles the administration of the web server, it is very important to give full access to the LOCAL SERVICE user for the certificate file.
Thus, right click to the certificate file, then access the “Security” tab.
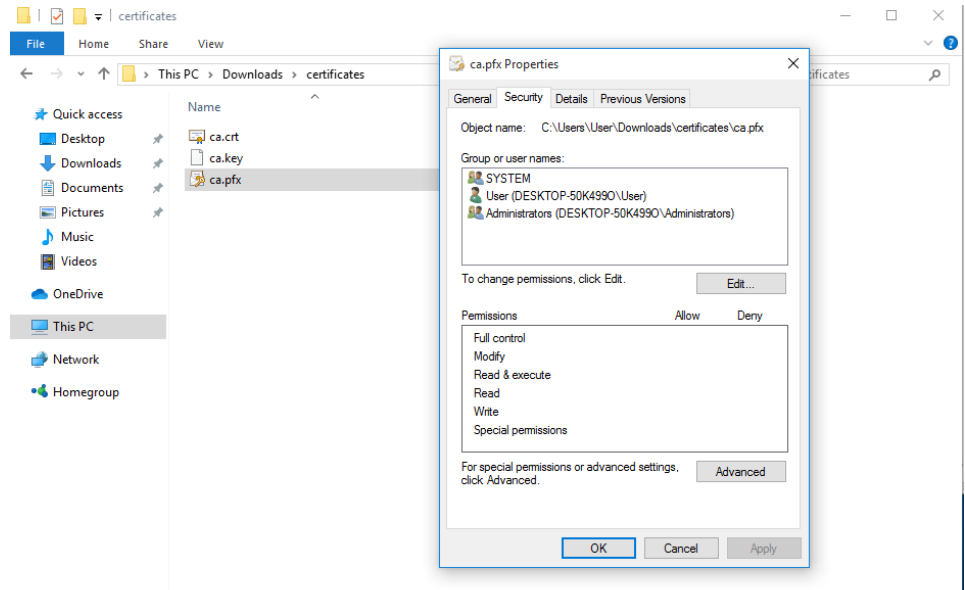
If there is not any LOCAL SERVICE group or user, click “Edit”, then “Add” to add a new group/user.
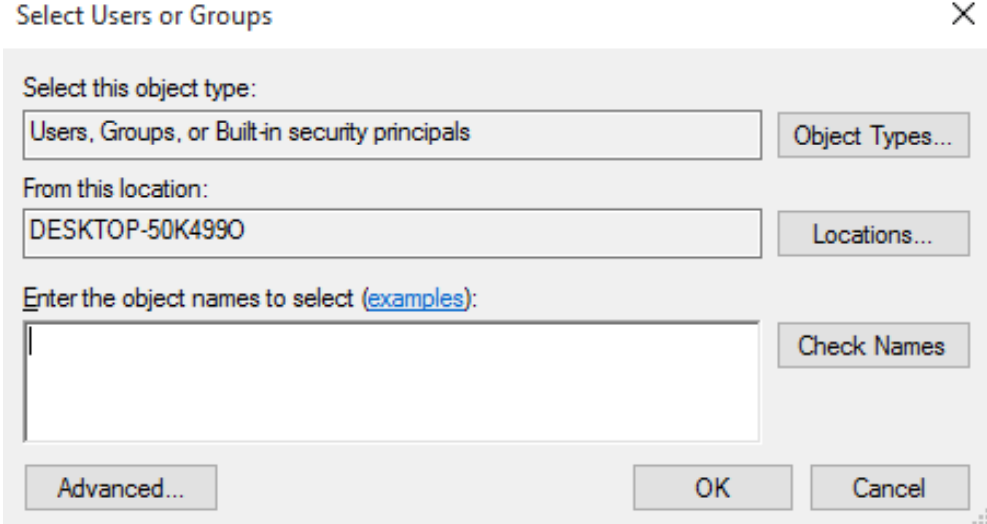
Furthermore, click “Advanced”, and once the new window opens click “Find Now” and from the list of Search results select “LOCAL SERVICE” and add it to the list of groups/users.
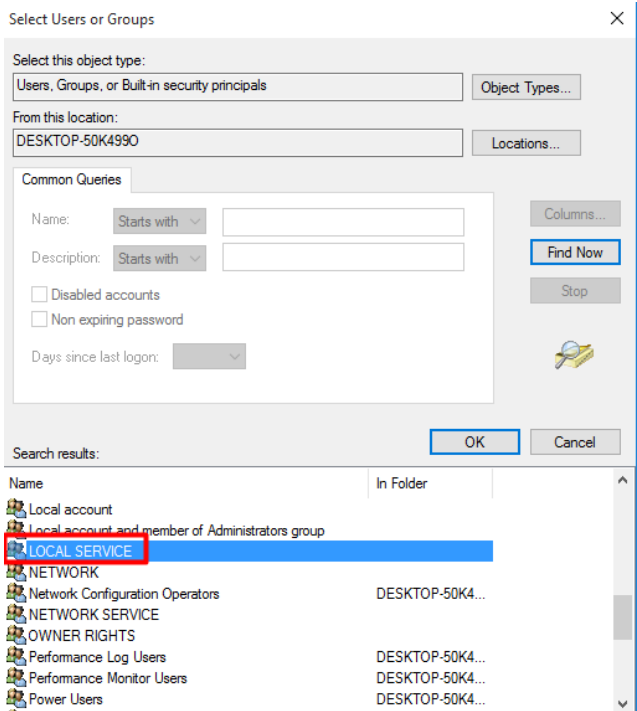
Once it gets added to the list, provide “Full control” permission for LOCAL SERVICE
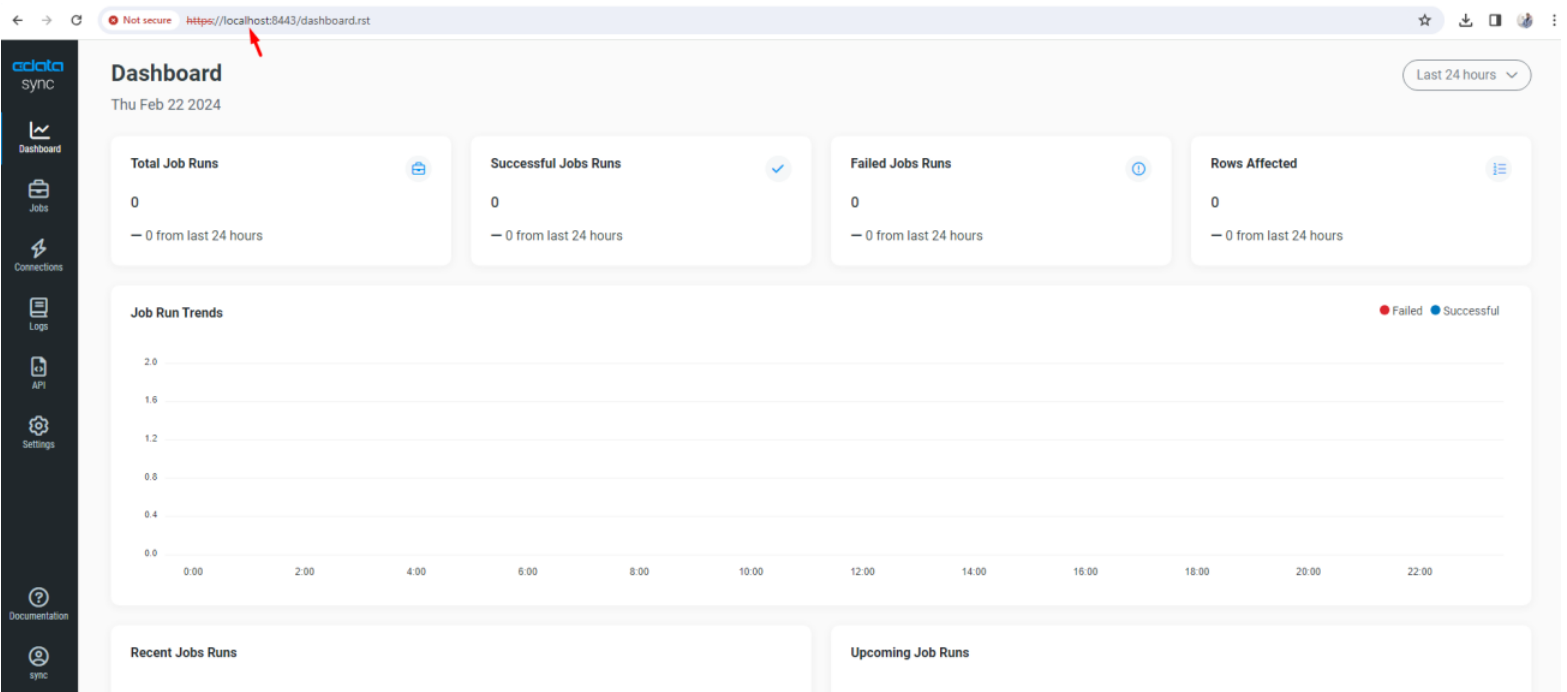
Once the steps are completed, restart “CData Sync” service and then access Sync at https://localhost:8443